A concerning trend is emerging among iPhone thieves who exploit a security feature known as the recovery key, jeopardizing users’ access to personal photos, messages, and financial data. Victims reported drained bank accounts after criminals gained entry to their financial apps. While this method is intricate, involving observing passcode entries or manipulating device owners, it highlights the urgency for enhanced user protection.
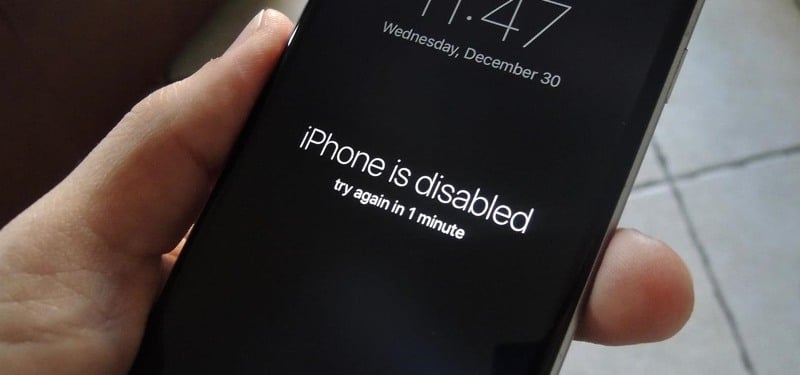
To execute this takeover, thieves must first physically steal the device, gaining access to the passcode. Subsequently, they manipulate settings, such as changing the Apple ID and disabling “Find my iPhone” to avoid tracking. The critical step involves resetting the recovery key, a complex 28-digit code designed to thwart online hackers. If successful, the original owner is left locked out of their account.
Apple acknowledges the severity of such incidents, expressing sympathy for affected users and emphasizing their commitment to user security. The company continually investigates and implements additional safeguards against emerging threats. However, on its website, Apple underscores user responsibility, stating that losing both the trusted devices and recovery key may result in a permanent account lockout.
Jeff Pollard, VP and principal analyst at Forrester Research, suggests Apple should enhance customer support options and authentication methods to counteract such security exploits. While users await potential improvements, there are several proactive steps they can take to mitigate the risk of falling victim to these sophisticated tactics. Learn how to bolster your iPhone’s security and protect against potential exploits.
Protection of Phone’s Passcode
Securing your iPhone’s passcode is paramount in safeguarding against theft and unauthorized access. Apple suggests utilizing Face ID or Touch ID, especially in public settings, to shield your passcode from prying eyes. Additionally, users can enhance security by opting for a longer, alphanumeric passcode that poses a greater challenge for potential intruders. Immediate passcode changes are crucial if there’s any suspicion of compromise.
Screen Time Settings
While not officially endorsed by Apple, an extra layer of defence can be added within the iPhone’s Screen Time settings. Originally designed for parental controls, this feature enables users to establish a secondary password. This secondary password becomes a mandatory requirement for anyone attempting to change an Apple ID. By activating this option, a thief would need to provide the secondary password before altering the Apple ID password, introducing an additional obstacle to unauthorized access.
Implementing these measures fortifies your iPhone’s security against evolving threats. Stay vigilant and proactive in protecting your device and personal information.
Taking Regular Phone Backups
Ensure ongoing protection by regularly backing up your iPhone through iCloud or iTunes. This practice guarantees the recovery of crucial data in the unfortunate event of an iPhone theft. Additionally, consider storing important photos and sensitive files in alternative cloud services like Google Photos, Microsoft OneDrive, Amazon Photos, or Dropbox. While this won’t prevent unauthorized access, it does minimize potential fallout by preserving essential data elsewhere.
By incorporating these proactive steps, you enhance your iPhone’s resilience against theft and potential data breaches. Stay ahead of evolving threats in the digital landscape by implementing these practical strategies.
In the rapidly evolving landscape of digital security, it’s crucial for iPhone users to remain vigilant against emerging threats. While the discussed strategies provide a solid foundation for bolstering device security, it’s equally important to stay informed about evolving security measures and potential risks. Regularly updating your knowledge on best practices and staying abreast of new security features introduced by Apple will empower you to navigate the digital realm securely. By cultivating a proactive mindset and incorporating the latest security measures, users can contribute to creating a robust defence against unauthorized access and data breaches. Remember, an informed and prepared user is the first line of defence in the ongoing battle for digital security.

